US Military, Non-US partners and potential users of Lockheed Martin’s (LMCO), an American aerospace & defense corporations, F-35 Lightning II, an all-weather multi-role stealth aircraft, have concerns about the planes data collection and sharing activities or cybersecurity posture. It appears these reports even led some countries to consider cancelling their participation. The F35’s Autonomic Logistics Information System (ALIS) has been at the center of these concerns. ALIS is an essential component described by LMCO as the “IT Backbone of the F-35”. Indeed, the system integrates maintenance, supply chain, combat-mission and threat analysis functions. The original objective of ALIS was a radical change to modern military aircraft management along the lines of predictive maintenance and other possibilities enabled by digitization. Essentially ALIS should allow for a holistic fleet management of the F-35 program (over 3000 planes are expected to be operated between 2023-2046) regardless of end-user by collecting and managing certain data for the benefit of all.
An ALIS SOU in deployable casings
Source: GAO Report, p,16 March 2020.
ALIS is a shared overarching system made of several components which early development activities date back to 2002. Each F-35 squadron has an ALIS package, which is connected to the global ALIS network. Devices in the aircraft track an incredible amount of data coming from of all its sensors during the flight. Once an F-35 returns to base, this data will be transferred to the ground-based part of ALIS via a portable memory device (PMD or “the brick”) or a laptop (PMD reader) which consists of the following bi-directional communication:
- A Standard Operating Unit ((SOU) – servers) will first download and analyze information after a mission. There are two SOU: one for classified aircraft-related data and one that supports unclassified aircraft-related data.
- The SOU sends data to the national Central Point of Entry (CPE). The CPE is a server unit (2 units that process and store classified and unclassified data) configured to provide software and data distribution for a nations’s entire F-35 fleet. The US has separate CPE’s for operational commands and training sites.
- From the CPE data is transferred to the central server (called Autonomic Logistic Operating Unit (ALOU)), based in the US, Texas, at Forth Worth run by LMCO. Again there are two servers that process and store classified and unclassified data. The system is also used to upload patches back to F-35 users.
Beside maintenance and logistic functions, the system is essential for mission planning and debriefing, as it also collects tactical data (flight routes, identified threats, hazards, etc.). This is then shared worldwide with all American and foreign F-35 operators.
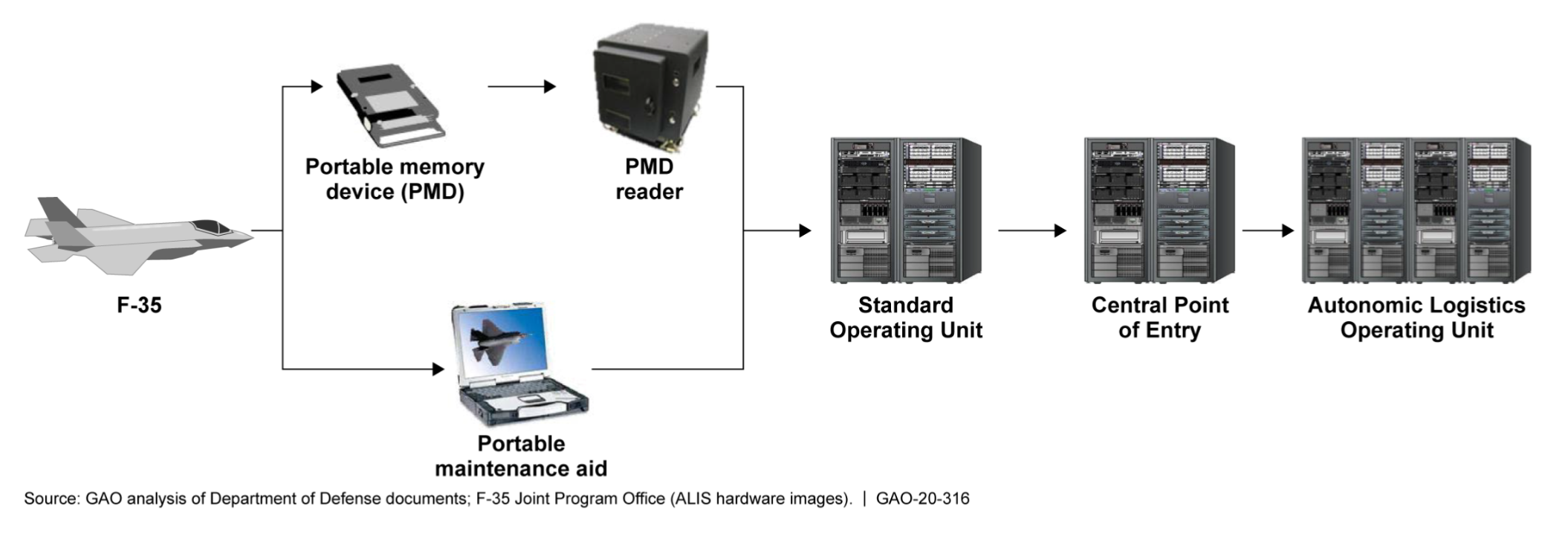
Unclassified data flow from F-35 through ALIS components.
Source: GAO Report, p. 10 March 2020.
ALIS is plagued with rising development costs, delivery delays (e.g. development testing was delivered eight years behind schedule in 2018) and technical shortfalls. What is more, Cybersecurity issues were identified and non-US users have concerns about data sovereignty and security. Access to the F-35’s software source code (over 25 million lines) remains a heavily contested issue elusive to be agreed to by the US government to be granted.
First, ALIS ultimately stores data on servers of a commercial company on U.S. soil. This places the data under the jurisdiction and within reach of the US government. Just like the US, other nations do not want share specific data (e.g. mission data) with anybody and have control of any data flows from a classified system to the outside.
Second, other nations depend on LMCO and the US to maintain their fleet of F-35. Vital upgrades could be put on hold, remotely challenging a country´s operational air force capability. As of today, only Israel has been allowed to run a totally independent system for the F-35 “Adir”.
Third, the F-35 is a software based aircraft relying on a broad software based platform in the air and on the ground. Reports state that ALIS is vulnerable to cyberattacks and data theft. It concerns the system itself but also LMCO. The latter’s network or any of the global military users and their commercial suppliers could present a broad attack surface with various entry points to bring down all of the F-35s. Patches could be delayed or compromised. Worst case scenarios include adversaries accessing highly classified mission data (referred to as Mission Data Files (MDF), undetected monitoring of mission planning or feeding of false data.
The US Department of Defense (DoD) awarded a $ 26 million contract to LMCO in 2018 to develop new version of ALIS, that includes a Sovereign Data Management (SDM) system which has been rolled out to Norway, Italy or the UK. They should be able to review and monitor data flow back to the US. Whether SDM can meet SECRET-level information assurance requirements is unclear.
Last year, DoD announced a rebranding of ALIS to ODIN (Operation Data Integrated Network). The ODIN kit is 75 percent smaller and weighs 90 percent less than the legacy SOUv2 ALIS hardware but its backbone will be in the DOD cloud ultimately provided by commercial hyper scalers such as Microsoft or Amazon. However, it is still not exactly clear which security features ODIN presents and how the data flow should be monitored. It has been described as a “firewall” or “software filter”. It has also been reported that Italy and Norway are designing an interim firewall at the Eglin Air Force base.
If SDM is only software or a combination of software filter and a tweaked firewall, cross domain solutions (CDS) could be the answer to the F-35 user base information security concerns. They present tested and well working high-assurance solutions that control bi-directional structured data flows via a Security Gateway / Guard / IEG present in the ALIS / ODIN solution architecture based on a whitelist principle. Parsers and the respective rulesets could easily be developed. Data sovereignty would be returned to F-35 nations.
F-35 foreign operators such Australia, Italy, Norway, the Netherlands, Canada, Israel, Japan, Denmark, Singapore, Belgium, Finland, South Korea and Poland could therefore find CDS optimized for F-35 data filtering an easy fix to their multi-year headaches. Implementing a cross domain solution could also address concerns that have been expressed by the Swiss government towards protecting classified data, after the decision was made to buy 36 F-35 aircrafts back in June 2021.
NATO lists products with these capabilities in the NATO Information Assurance Product Catalogue (NIAPC).